Police and Protect your Network
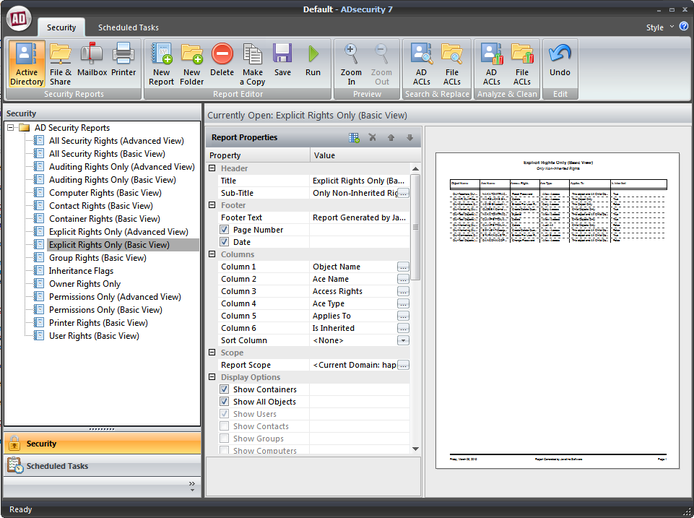
ADsecurity gives administrators the ability to easily document, find, and fix their network’s security. And with a simple, client only installation, ADsecurity provides network security management without servers, agents, or other complications.
Scenario:
Your company is preparing for a SOX audit. You have a set of standards you have maintained for your network and now is your chance to show that you’re network is top of the line when it comes to security. With ADsecurity at your fingertips you’ve already located and corrected problems like deleted users and invalid objects on your ACLs. Now with a few mouse clicks you can easily report on all your Active Directory ACLs, file and share ACLs, and even your Exchange mailbox ACLs.
ADsecurity highlights security issues so you can fix them.
It is important for your company to maintain separation of data. You don’t want all employees to have access to accounting’s data and it is imperative that the personnel data only be accessible to HR. Prior to ADsecurity you’ve spent hours fumbling with spreadsheets and screenshots to document who has access to what folders.
And of course, this information is the first thing the auditor wants to find out: i.e. who has access to what. With ADsecurity you can now pull up a shared permissions report in seconds that will give you all the data you use to maintain on your spreadsheet. The auditors are supplied with a report that you e-mailed automatically via ADsecurity tools, and you’re off to your next task.
Scenario:
Your company is preparing for a SOX audit. You have a set of standards you have maintained for your network and now is your chance to show that you’re network is top of the line when it comes to security. With ADsecurity at your fingertips you’ve already located and corrected problems like deleted users and invalid objects on your ACLs. Now with a few mouse clicks you can easily report on all your Active Directory ACLs, file and share ACLs, and even your Exchange mailbox ACLs.
ADsecurity highlights security issues so you can fix them.
It is important for your company to maintain separation of data. You don’t want all employees to have access to accounting’s data and it is imperative that the personnel data only be accessible to HR. Prior to ADsecurity you’ve spent hours fumbling with spreadsheets and screenshots to document who has access to what folders.
And of course, this information is the first thing the auditor wants to find out: i.e. who has access to what. With ADsecurity you can now pull up a shared permissions report in seconds that will give you all the data you use to maintain on your spreadsheet. The auditors are supplied with a report that you e-mailed automatically via ADsecurity tools, and you’re off to your next task.
ADsecurity Features
Reporting at your fingertips:
• Reports on Security rights for Files and Shares, Active Directory Objects, Exchange Mailboxes, and Printers
• Includes dozens of standard reports
• Create custom reports without scripting
• Schedule reports to run at your convenience
• Filter for the information you need
• Save report data in CSV or PDF format
• Schedule reports to run automatically
• Automatically Email reports via SMTP or Exchange
Analyze and Clean ACLs:
• Scan through the ACLs on Files, Shares and Active Directory Objects
• Find empty and missing ACLs
• Find invalid or deleted SIDs in ACEs
• Find individual user names appearing in ACLs and Owner fields.
• Find Computer names appearing in ACLs and Owner fields
• Remove invalid or unknown SIDs from ACEs with undo capability
Search And Replace ACLs:
• Search through the ACLs on Files, Shares and Active Directory Objects
• Replace ACEs in the Owner Field, in the ACL, or in both
• Replace matching ACEs or remove them
• Create an Undo file for reverting ACLs back to their original state
• Reports on Security rights for Files and Shares, Active Directory Objects, Exchange Mailboxes, and Printers
• Includes dozens of standard reports
• Create custom reports without scripting
• Schedule reports to run at your convenience
• Filter for the information you need
• Save report data in CSV or PDF format
• Schedule reports to run automatically
• Automatically Email reports via SMTP or Exchange
Analyze and Clean ACLs:
• Scan through the ACLs on Files, Shares and Active Directory Objects
• Find empty and missing ACLs
• Find invalid or deleted SIDs in ACEs
• Find individual user names appearing in ACLs and Owner fields.
• Find Computer names appearing in ACLs and Owner fields
• Remove invalid or unknown SIDs from ACEs with undo capability
Search And Replace ACLs:
• Search through the ACLs on Files, Shares and Active Directory Objects
• Replace ACEs in the Owner Field, in the ACL, or in both
• Replace matching ACEs or remove them
• Create an Undo file for reverting ACLs back to their original state